A Staple of the Corporate Domain
Many IT administrators consider Group Policy as the foundation for any corporate IT network. When rolling out any IT standard or security policy across the user base, Group Policy has always been the go-to solution. Group Policy enables IT teams to apply consistent and standardized policies across enterprise environments. These changes thanks to GP do not require complex changes to the registry editor or reliance on individual effort. Until recently, Group Policy Management had been capable of addressing virtually any policy enforcement needs within any corporate IT environment.
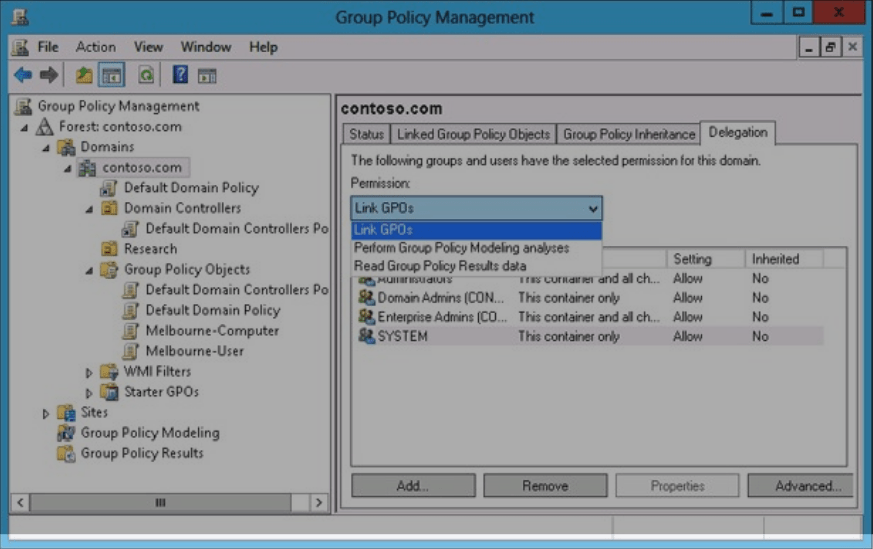
Example screenshot of Group Policy Management
Then remote work and the use of personal devices (BYOD) were introduced into the fray. For the first time in over a decade, GPOs could no longer keep up with an emerging trend: the increasing demands of a work-from-anywhere user base. Folks needing to access sensitive data from anywhere and on any device creates complexities that must be overcome to successfully apply company policy.
Limited by Distance
To start with, the challenge of modern work is limited by distance. Even if a device is corporate-owned, the first question is how it can check in with the domain controller to receive the latest GP update. One option is for the device to connect back to the corporate domain via VPN. However, it is difficult to ensure that remote workers will regularly do this and that the GP update will apply to the device since this process normally only takes place at login. Attempting to follow these steps is an uphill battle from an administrator’s perspective.
Limited by Device
As an administrator, you may have cleared the hurdle of distance, but now face the challenge of BYOD. How do you control access to company data on non-company devices like personal laptops, tablets, and mobile phones? Today’s work culture emphasizes working anywhere on a device of one’s choosing, which makes managing personal devices a roadblock for Group Policy. Years ago, ActiveSync only allowed remote wiping of mobile devices, which was a primitive form of control for corporate accounts. Administrators had limited tools for remote device management, which did not balance corporate security policy with the demands of the remote user base. This limitation makes it clear that Group Policy cannot meet the needs of modern administrators.
Introducing Microsoft Intune
Intune initially debuted in 2011 as Windows Intune and was a service portal on top of the Microsoft Malware protection engine. In the few years following its debut, incremental changes were made to the solution to begin shaping the product it would become. At that time, nobody could’ve truly envisioned this modern work era in which we now find ourselves. An era that was primarily ushered in by a global pandemic that has changed our society in so many ways. Our expectations for technology have never been higher and that has dramatically increased the pressure on IT admins across the globe to keep up with demand.
Embracing Change
Change can be hard, and for many admins, ditching their established policies can be daunting. However, Microsoft is making it easy to leverage Office 365 for email hosting and is doing the same with Intune. In a few years, we’ll view localized legacy domains like on-premises Exchange servers – a thing of the past. We’ll be happy to no longer endure the headaches, and constraints of a management plane created for a bygone era.
Enhanced Capabilities
Intune’s policies can be broken down into 4 main types:
Configuration Profiles:
These policies enable device management and configuration of device settings. For instance, IT can configure a Windows 11 device to join a specific Wi-Fi network without requiring the user to input credentials. Additionally, IT can enforce corporate background wallpaper and restrict the addition of personal OneDrive accounts to prevent data exfiltration by rogue employees. The available configuration settings for a given device are numerous.
Compliance Policies:
Compliance policies are essential for determining whether devices adhere to the organization’s standards. IT defines these rules, which can include requiring an approved anti-virus solution with updated virus definitions. Rules may also address enabling Microsoft Defender, having a compliant TPM chip, or requiring BitLocker encryption. If a device is deemed non-compliant, specific actions can be triggered. Actions include: marking the device as non-compliant after a specified period, sending a notification email to an admin, or retiring the device.
Security Baselines:
These are groups of security policies that can be configured for a particular type of device from one location. For instance, on a Windows 10+ device, IT can enforce enabling BitLocker, prevent end-users from storing passwords using the browser’s built-in password manager, block auto joining of Wi-Fi networks, or require a password after a machine wakes from sleep. Currently, there are no security baselines for operating systems other than Windows.
Conditional Access:
These policies specifically outline login requirements. Furthermore, they outline where users can log in to access any sensitive information in M365 and Azure. These powerful policies allow a modern administrator to level the playing field in today’s world of modern work.
Conclusion
We are at a point where Intune has proven to be superior to Group Policy in today’s IT environments. Admins are now at a crossroads: embrace a superior solution for policy, security, and compliance management via Intune or remain stuck in a feature-limited console by continuing to leverage Group Policy Management. We at Nerdio have talked to many admins, MSPs, and industry leaders and the choice is clear. Intune is the superior solution and will continue to be for years ahead.
To learn more about Microsoft Intune and to schedule a demo option visit: getnerdio.com/Intune